Security.VCL
Posted on 2009-08-12
Edward Bjarte Fjellskål, Kacper Wysocki and myself have been working on Security.VCL, a small (for now?) project to imitate much of the functionality that mod_security has in VCL.
The basic idea is this: You're already running Varnish, and you want to add some basic filtering of Bad Things. Varnish is Quite Fast[tm] when it comes to parsing headers, so doing so in VCL makes sense. VCL also makes it easy to include other VCL files as they are just appended, so let's write a VCL that detects some common script-kiddie stuff. The typical example would be someone trying to access "../../" or similar.
Kacper made a script to re-write most of the mod_security rules to VCL, I made the basic framework and Edward has written several customized rules. The flexibilty that VCL offers makes it easy to customize security.vcl in a simple manner. We've yet to write any backend-magic, but in theory, you could easily block clients in your firewall, log them or just redirect them. We supply a couple of examples of this in the main VCL.
So far, the major drawback is that Varnish is not designed to analyze the content of POST requests.
At the moment, Security.VCL is a working (internal) PoC, and we've yet to decide what to do with it. But the concept is quite interesting, if I may say so myself.
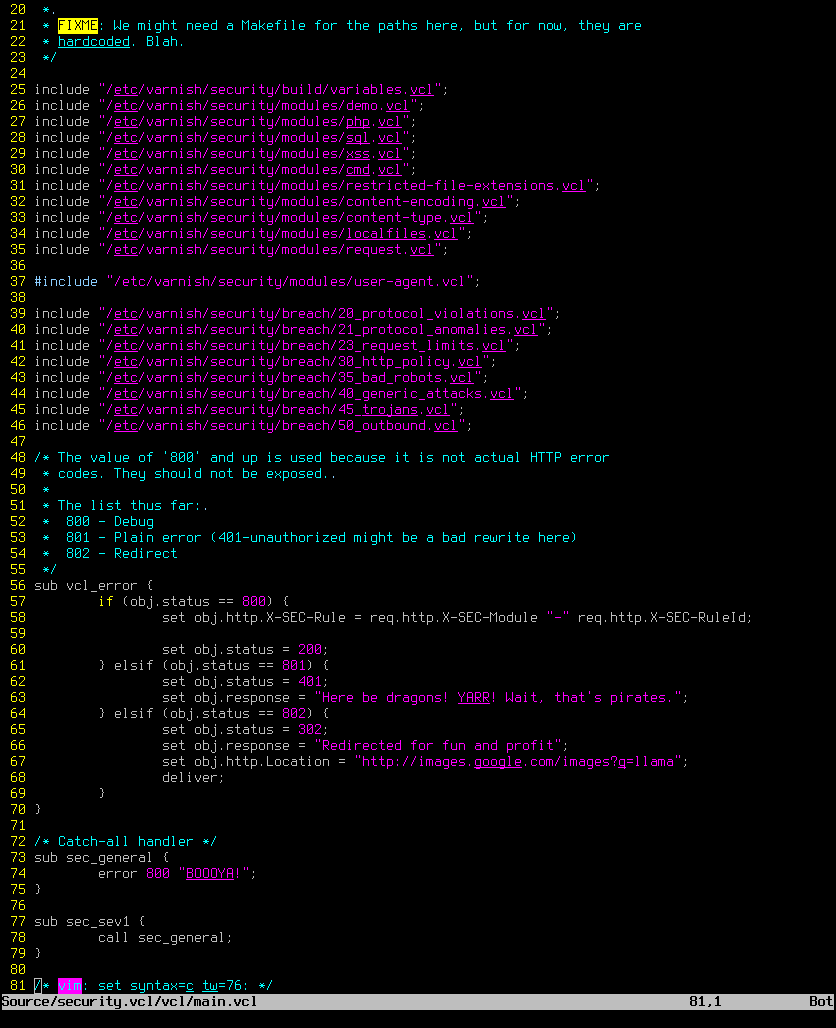
Since we haven't done a release yet, we figured we'd post a (mostly useless) screenshot of a random portion of the code. Unfortunately, I'm not quite cool enough to use green fonts. So grey will have to do: